At GitHub, we believe that investing in the security of your codebases should be straightforward, affordable, and scalable. Today, we’re rolling out standalone GitHub Advanced Security products for GitHub Enterprise customers. This aligns with our ongoing mission to help organizations of all sizes secure their code with the flexibility they seek.
Getting started as an existing GitHub Advanced Security customer
Existing GitHub Advanced Security customers with plans subscription-based plans can choose to transition at renewal. Customers with pay-as-you-go, metered-based plans can transition at any time. Please reach out to your GitHub or Microsoft sales account team for details.
Customers on subscription billing can migrate to either a standalone subscription or a standalone metered plan. For pricing details, please contact your account representatives.
How do I right-size enablement for my enterprise?
Customers transitioning before May 2025 can work with their account teams on right-sizing enablement for their enterprise across both Secret Protection and Code Security. All repositories will have both Secret Protection and Code Security enabled at the time of transition, regardless of your contractual plan.
Customers on contractual plans limited to secret scanning features will be able to optionally choose to transition with only Secret Protection enabled (and Code Security disabled) for their enterprise starting in May 2025.
When will the standalone plans be available for Enterprise Server?
Standalone SKUs will be available for Enterprise Server customers starting with GHES 3.17. To use metered billing, GitHub Connect is required.
Getting started as an existing GitHub Advanced Security self-serve customer
For existing self-serve customers, instructions on how to transition to the new GitHub Advanced Security plans will be announced over the next 30 days. You’ll receive an email notification when the new plans are available to your enterprise. Transitioning to the standalone plans will be self-serve and optional.
Getting started for new customers
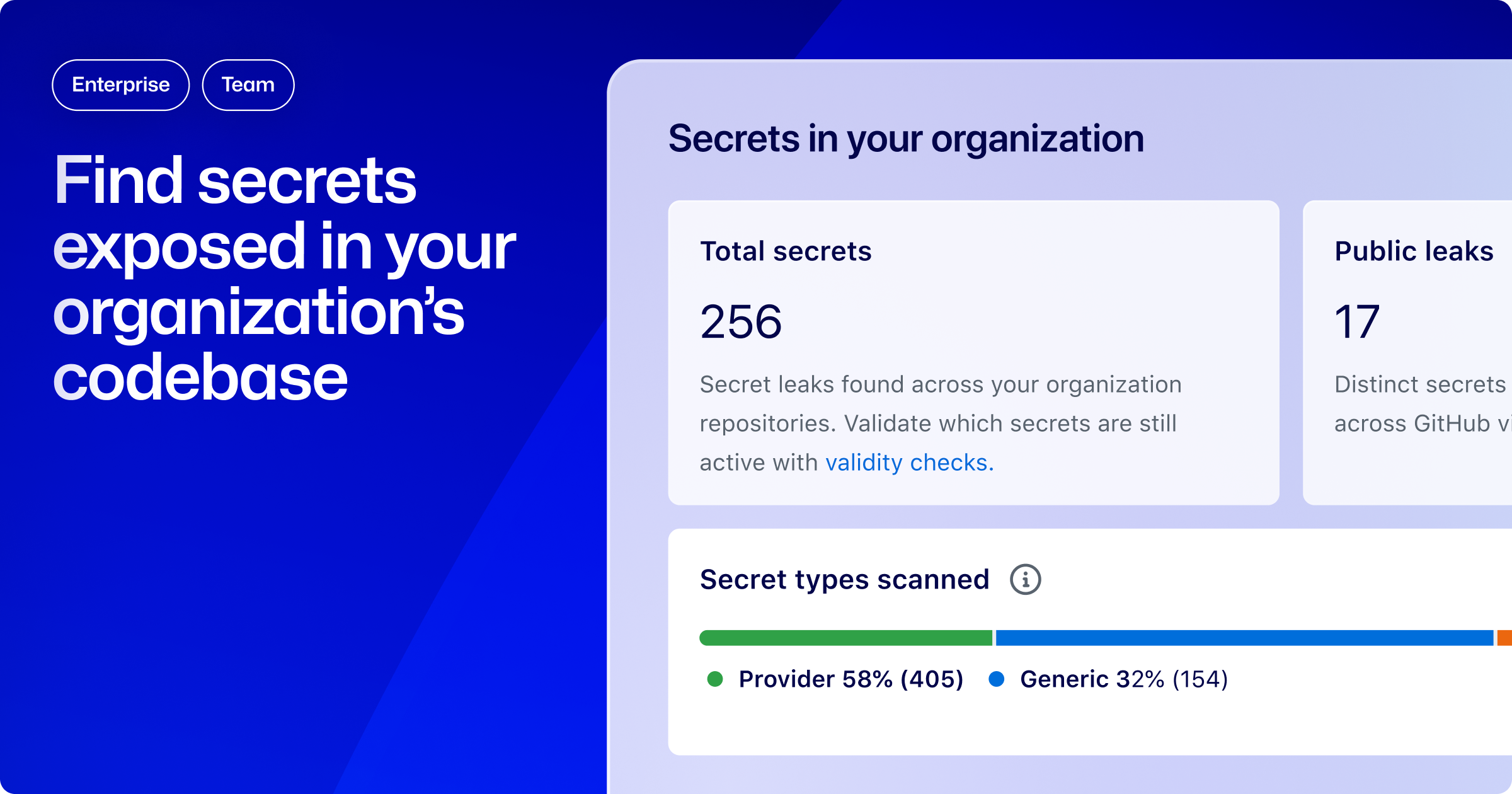
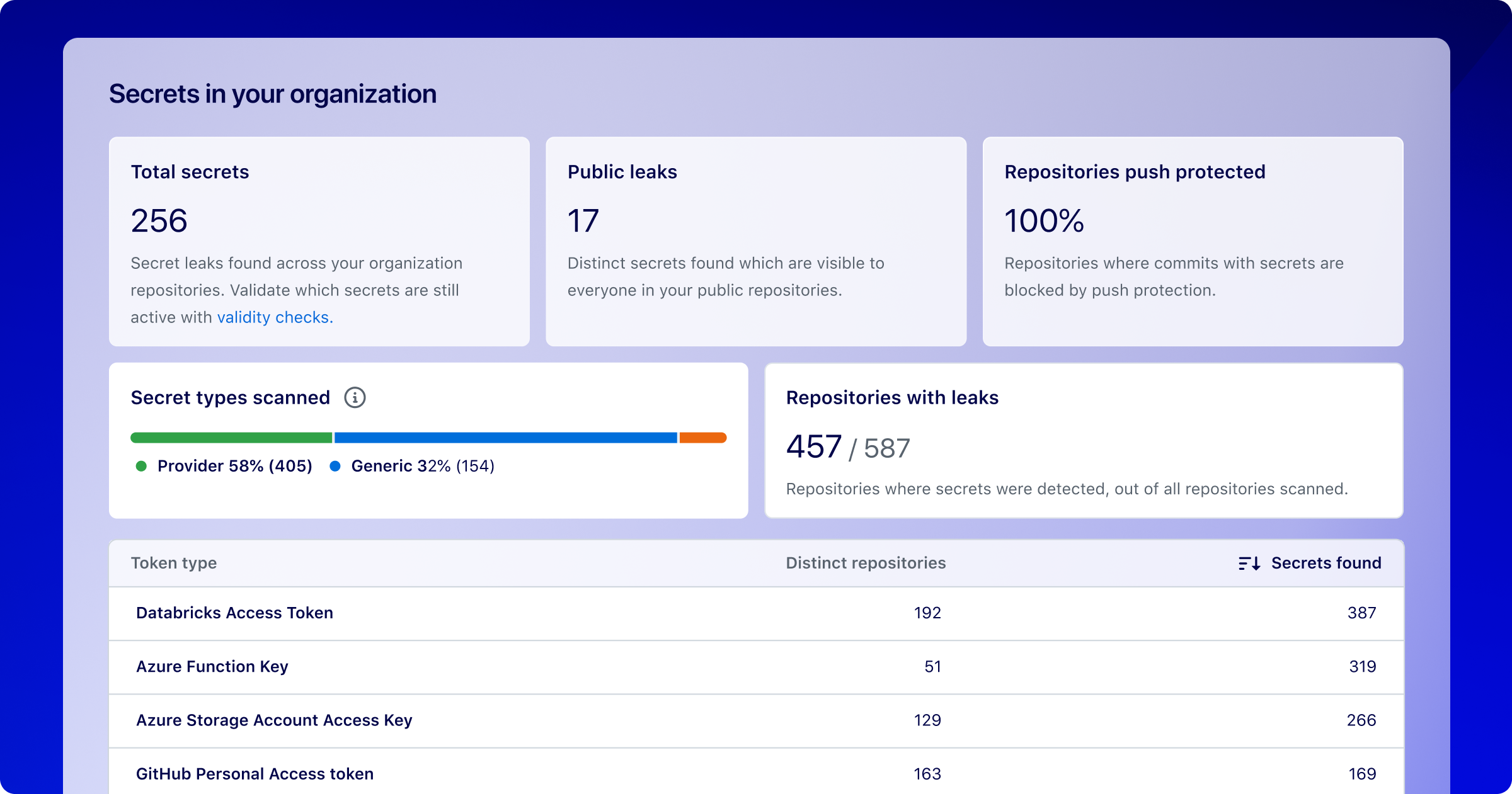
Starting today, GitHub Enterprise customers without an existing GitHub Advanced Security plan can self-serve purchase both Secret Protection and Code Security. To get started, admins can navigate to Advanced Security under their enterprise, organization, or repository settings. From this page, you can choose to enable and purchase Secret Protection or Code Security features.
Learn more about enabling GitHub Advanced Security for your enterprise.
Trialing GitHub Advanced Security
You can try the new standalone SKUs before committing. Contact your account team for more details. Alternatively, you can get started with a GitHub Enterprise trial.
Talk to someone from GitHub
In addition, Enterprise customers are welcome to reach out to their existing account team or request a demo from someone at GitHub.
Learn more and share feedback
Learn more about Secret Protection and Code Security, or share feedback by joining the discussion in GitHub Community.